Data privacy and collection
Spectra Assure Portal is a cloud-based solution hosted on Amazon architecture (AWS).
This page explains what data is collected and how it is handled by ReversingLabs when you use the Spectra Assure Portal to analyze your files.
ReversingLabs prioritizes the privacy and security of your data, and collects only the essentials required for the optimum user experience and product performance.
Consequently, the following data is never collected or sent anywhere by the Portal:
- your policy configuration settings. Policy controls are processed and applied on organization and group level on your Portal instance.
- your analysis reports. Reports in all formats are stored only on your Portal instance and can be shared with people inside and outside of your organization.
- your Personal Access Tokens for the API. They are only used for communication with the Portal instance via the API
- usernames, passwords, and tokens provided when using URL import on File Stream and Projects pages. They are forwarded directly to the service that requests authentication to start the file download.
When your data is collected by the Portal, it is sent only to the official ReversingLabs servers listed in the next section.
Data privacy conditions and exceptions described on this page apply only for the default Portal instances from official ReversingLabs sources. Different conditions may apply if you're using Portal through CI/CD integrations.
ReversingLabs cloud endpoints
The Portal sends your data only to the following ReversingLabs resources:
data.reversinglabs.com
This endpoint is often referred to as "the ReversingLabs cloud".
The same endpoint is also accessed by the Portal to interact with Spectra Community APIs when evaluating packages from community repositories.
The following policies rely on the data from Spectra Community APIs:
TH30101 - Detected presence of software components that had a recent malware or tampering incident.TH30102 - Detected presence of software components that are quarantined in the community package index.
TH30103 - Detected presence of software components that were removed from the public package repository.
TH30104 - Detected presence of software components that had a recent package version removal incident.
TH30105 - Detected presence of software components that were recently published to the public package repository.
TH30106 - Detected presence of software components that have low popularity or number of downloads.
TH30107 - Detected presence of software components that are rarely included by other public software packages.
TH30108 - Detected presence of software components that are impersonating popular software packages.
TH30112 - Detected presence of software components without a declared source code repository.
TH30113 - Detected presence of software components with unusual package versions.
Data collected during file analysis
When you use the Portal to scan software packages, the following data is sent to the ReversingLabs cloud:
Hashes of analyzed files and their components
Spectra Assure Portal calculates MD5, SHA1, and SHA256 hashes for every analyzed software package and for each component in the analyzed software package. Hashes are sent to the ReversingLabs cloud to look up file reputation information and retrieve classification for the software package and/or its components using ReversingLabs Spectra Intelligence as the classification technology. Based on this cloud lookup, components can get the "Verified by Cloud source" status (indicated in the Verified column of the SBOM section in the report).
License type, version, and status
Spectra Assure Portal verifies that the installed license is valid and checks its current status and usage in the ReversingLabs cloud. The available analysis capacity is updated to account for the file size of the analyzed software package. If you are using both the Spectra Assure Portal and
rl-secure, your license is shared between the two products. Any analysis capacity you spend while analyzing files with the Spectra Assure Portal is automatically reflected in your Portal instance.
This data is collected:
- every time the Portal is used to analyze files (either on File Stream or the Projects page),
- when reanalyzing files (after modifying the configuration or after the Portal instance is updated to the latest version)
The contents of your software packages are never sent anywhere by the Portal. All supported file types are statically analyzed with the Portal and rely on threat detection technologies embedded in the analysis engine.
Data encryption
On the Portal, all data is protected using industry-standard encryption protocols:
- TLS 1.2, as it travels to storage (encryption in transit)
- AES-256, when stored (encryption at rest)
All encryption keys and secrets are carefully managed through our Key Loading Management System (KLMS) to ensure maximum protection.
More details on how your data is protected can be found in the official Amazon S3 documentation.
Database backup
All data on your Portal instance is stored in the designated database, as well as the S3 bucket. Data retention period varies depending on which page of your Portal instance the data is stored.
On File Stream, the uploaded files are available for 90 days, after which they're automatically removed from your Portal instance and the S3 bucket. The Projects page does not have a set retention period - the data is retained as long as a Portal instance is active. After shutting down a Portal instance, all the retained data, including their backup copies, is deleted. When a user deletes a file manually, it's immediately removed from the Portal and the S3 bucket it's stored on.
There are two ways of backing up the database - full backup and incremental backup. Full backup copies all stored data, regardless of whether it has changed. On the other hand, incremental backup copies only the data that has changed since the last backup of any kind (usually the last incremental backup). The full backup method is used immediately before and immediately after version upgrade, while the incremental backup method is used on a daily basis.
All backup procedures in place are checked annually.
SSO
When SSO is configured on a Portal instance, users do not need to create a separate account for the Portal. SSO allows them to use only one set of credentials (usually their username/organization email and password) to log in to various applications and services.
Every time a user wants to log in to the Portal by using SSO, their identity needs to be determined on the identity provider (IdP) side. To do that, the Portal sends only the user email address to the identity provider.
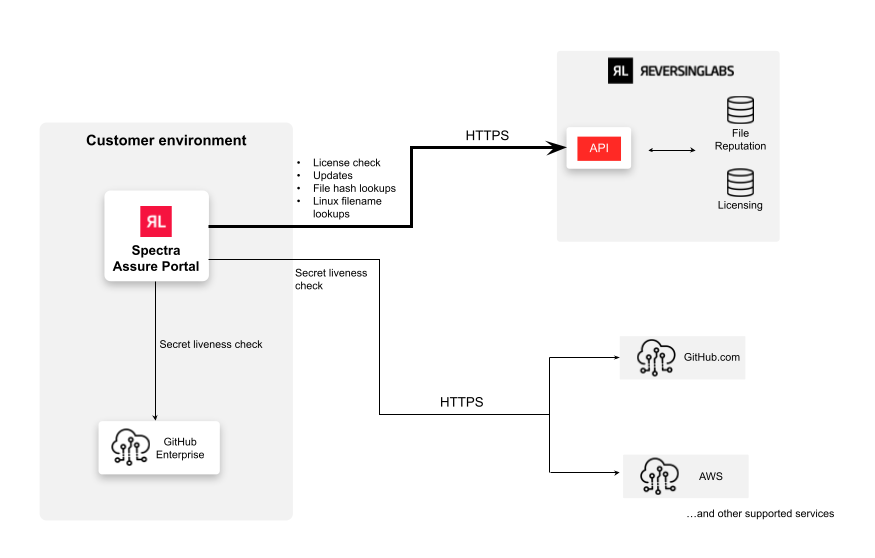
Live secret validation
The live secret validation (secret liveness check) feature enables the Portal to automatically check if any of the detected secrets in your packages are still considered active and susceptible to abuse. This feature is enabled by default on all Portal instances and cannot be disabled.
The secret liveness check is performed by the Portal during file analysis. When a secret is detected in your software, the Portal automatically recognizes which service it belongs to and determines its type (for example, a GitHub access token).
If the service is supported by the live secret validation feature, the Portal then pings the least-privilege public endpoint of that service and checks if the detected secret can be used to authenticate to the service.
Secrets are never sent for validation through ReversingLabs servers. They are sent to the appropriate service endpoint directly through your network. This happens only after the connection is verified as secure by checking the pinned certificate.
Some of the secrets in your packages may have the Exposed status in the analysis reports. This status indicates that the secret was previously recorded in the ReversingLabs cloud at least once.
Exposed secrets are detected based on file hashes. If a file is uploaded to the ReversingLabs cloud as public, all the secrets it contains are public as well.
Data collected for usage analytics
For the purpose of ascertaining the usage of certain features across the Portal, it's tracked:
- how many times the action has been performed
- when has the action last been performed
The statistics is collected for all available actions across Portal pages (File Stream, Projects, Report, Policies, and Organization settings), as well as the general user actions, such as login, password update, PAT generation/revoking, etc.
To get more details on how ReversingLabs collects, uses, stores, and protects personal data, check out the official ReversingLabs privacy policy.
Data privacy with Portal integrations
The Portal supports a number of official integrations created by ReversingLabs to facilitate automation use-cases and CI/CD workflows.
By default, data collected by the Portal is not transferred to any third parties unless explicitly configured in the CI/CD integration settings.
Depending on your CI/CD service and workflow configuration (self-hosted or cloud-based), additional data may need to be stored externally or shared with third-party services to enable Portal functionalities for the integration.
That data may include, but is not limited to:
- Personal Access Token for authenticating requests to the Portal
- a list of projects and packages on the Projects page of your Portal instance
- analysis reports.
For specifics, consult the documentation for the Portal integrations you intend to use, as well as the official documentation of your CI/CD services.
AI model training and customer data
ReversingLabs never uses customer data to train or improve its AI models.
Any AI features, such as generating vulnerability summaries, are designed to function without using or processing customer data. In addition to that, customer data processing systems are strictly separated from AI model training workflows to ensure confidentiality and protect your information.
If you have any further questions or concerns regarding data collection and privacy, contact ReversingLabs Support for assistance.